It has become some sort of a running gag in the cybersecurity communication that operational technology (OT) networks and industrial control systems (ICS) are notoriously insecure. However, most reports on this are limited to assumptions and general warnings.
For this reason, we reviewed the results from nearly two dozen Rhebo Industrial Security Assessments (RISSA) that we conducted in 2022, primarily at German energy companies as well as some industrial companies.

During a RISSA, the OT infrastructure and communications are investigated specifically with the aim of identifying anomalies and vulnerabilities. For this purpose, the OT monitoring with anomaly detection Rhebo Industrial Protector is integrated via switch port at a central point in the OT without affecting the OT itself. Next, the communication in the OT is recorded passively over an average period of 14 days. Rhebo OT experts then analyze the communication logging and document:
- anomalies, risks, misconfigurations;
- the active systems and devices as well as their connections and respective connection quality (Fig. 1).
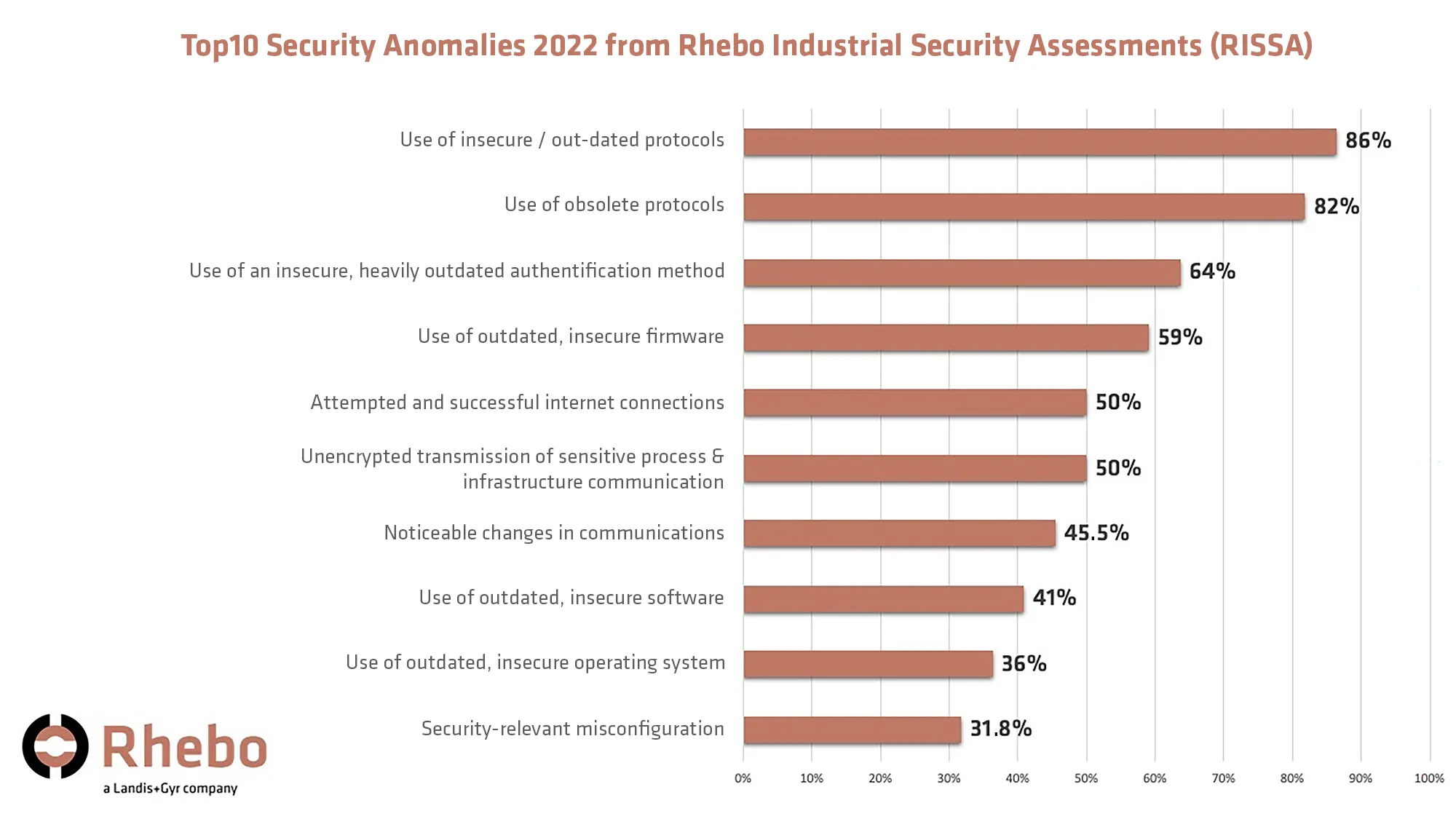
On average 18 categories of anomalies were identified in each risk analysis. While this might sound low, often anomaly categories were recorded several times in one single RISSA. This means that the absolute number of anomalies identified in the OT networks is generally much larger than the aggregated average value presented in this review.
No industrial control system is secure
The results show that a large proportion of risks and anomalies involve legacy issues. In addition, there are communication processes of devices and systems that often run as default settings, thus unbeknownst to the operators. Also noticeable are implausible - and thus potentially dangerous - changes within the otherwise stable, repetitive and deterministic OT communication (Fig. 1).
The following table explains the Top10 anomalies in detail in terms of their source and risk.
Anomaly categoryRiskLegacy protocols
The lack of authentication and/or encryption capabilities of legacy protocols allow attackers to extract valuable information from the infrastructure that can be used to propagate an attack.
Obsolete protocols
Devices and systems communicate via protocols that are obsolete in the respective OT infrastructure. Typically, this communication also has no operational relevance, but continues to run automatically due to default settings. Often, these are multicast messages with which devices try to advertise their own services and software versions. Unused protocols are potential attack vectors and should be disabled.
Outdated insecure authentication method
The affected authentication method has not received support from the vendor for over ten years. The password hashes can be decrypted within a short time. Furthermore, the method is responsible for frequent zero-day vulnerabilities in systems from this vendor.
Vulnerable firmware, software or operating systems
Outdated firmware, software and operating systems usually have unpatched vulnerabilities that can be exploited by attackers. In particular, outdated firmware on network components poses a widespread problem.
Attempted and successful internet connections
Successful connections from OT components to external servers can represent an information leak in a company's network or provide attackers with an effective access point.
Unencrypted transmission of sensitive infrastructure communication
Communications that transmit passwords as plain text provide attackers with valuable information for lateral movement, account takeover, and threat propagation.
Noticeable communication changes
Industrial communication is characterized by repetitive and deterministic patterns. Sudden drops, load peaks or even a changed traffic pattern can be indications of active intervention in the behavior of a system or device.
Risky misconfigurations
Certain misconfigurations enable attackers to intercept sensitive information or launch man-in-the-middle attacks. These include configuration via DHCP both in the network and on components looking for a corresponding server. Other noticeable misconfigurations include router advertisements and source routing.
Generally, attackers can only exploit these risks if they already have access to the network. Nevertheless, they form a valuable arsenal that enables attackers:
- to move laterally in the network;
- to understand the infrastructure;
- to consolidate and extend their access as well as
- to propagate their attack.
A RISSA provides operators with the visibility and know-how to detect these pre-existing risks within a very short period of time as well as to mitigate them.
From initial risk analysis to continuous OT security
Typically, Rhebo Industrial Protector remains in the OT after the risk analysis has been completed. It is directly set to continuous operation to allow for continuous OT monitoring with anomaly and intrusion detection. Anomalies that were identified during the risk analysis, but have not yet been resolved, can be given "Monitor" status in the OT monitoring system. This allows managers to track them and monitor their frequency until a solution is found.
The OT monitoring system with anomaly detection enables security managers and operators to continuously monitor all OT communication, and to identify anomalies in real time. As a result, industrial companies and critical infrastructures know exactly what is happening in their OT and can mitigate any deviations – from technical error states to orchestrated cyberattacks – at an early stage. In OT environments where attacks move slowly, this capacity of early detection decides between downtime and process continuation.
